You should never share your account, In the event you share your account so technique will right away delete your account.
SSH is a regular for secure distant logins and file transfers more than untrusted networks. In addition, it gives a method to secure the info visitors of any presented software using port forwarding, essentially tunneling any TCP/IP port over SSH.
Search the world wide web in comprehensive privacy though concealing your real IP deal with. Preserve the privateness of one's area and prevent your Online provider provider from checking your on-line exercise.
All ssh tunnel accounts are Geared up with endless bandwidth around 1Gbps. To utilize SSH tunneling, you'll want to have an SSH consumer set up on your neighborhood Laptop or computer and access to an SSH server. It is possible to then use the SSH client to ascertain a secure link towards the SSH server and configure the tunneling configurations. Record SSH Shopper Apps
Though SSH3 shows promise for faster session institution, it remains at an early evidence-of-thought phase. As with all new elaborate protocol, qualified cryptographic critique about an prolonged timeframe is needed in advance of acceptable protection conclusions is often designed.
Even though SSHv2 defines its very own protocols for person authentication and secure channel establishment, SSH3 relies over the robust and time-examined mechanisms of TLS one.
Proxy leap (see the -proxy-soar parameter). If A is an SSH3 Fast Proxy Premium consumer and B and C are both equally SSH3 servers, you are able to link from A to C using B like a gateway/proxy. The proxy employs UDP forwarding to forward the QUIC packets from the to C, so B can not decrypt the targeted visitors AC SSH3 traffic.
But you can also try out a Trial Account very first ahead of essentially shopping for it with a specific closing date. It's also possible to freeze an account to prevent billing if not use for the subsequent several hrs. Sense free to deal with your account.
Since the demand for effective and real-time interaction grows, the usage of UDP Customized Servers and SSH more than UDP is starting to become increasingly applicable. Leveraging the speed and minimalism of UDP, SSH about UDP gives an thrilling new method of secure remote access and details transfer.
Connectionless: UDP is connectionless, which means it doesn't create a persistent connection concerning the
Secure Distant Obtain: SSH provides a secure channel for distant entry, allowing for end users to hook up with and deal with methods from any where by having an internet connection.
You can find many alternative tips on how to use SSH tunneling, depending on your needs. For example, you might use an SSH tunnel to securely obtain a distant network, bypassing a firewall or other safety measures. Alternatively, you might use an SSH tunnel to securely obtain a neighborhood network resource from the remote place, for instance a file server or printer.
SSH can even be utilized to transfer data files in between programs. This is the secure method to transfer sensitive files, including money details or customer details. SSH employs encryption to safeguard the information from currently being intercepted and browse by unauthorized people.
Premium Company also Premium Server aka Pro Server is really a compensated server using an hourly payment method. Using the very best quality server as well as a limited amount of accounts on Every single server. You're needed to leading up to start with in order to take pleasure in the Premium Account.
 Brandy Then & Now!
Brandy Then & Now! Marla Sokoloff Then & Now!
Marla Sokoloff Then & Now!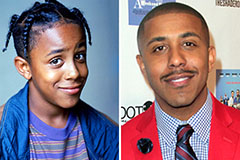 Marques Houston Then & Now!
Marques Houston Then & Now! Freddie Prinze Jr. Then & Now!
Freddie Prinze Jr. Then & Now! Andrew McCarthy Then & Now!
Andrew McCarthy Then & Now!